Hello,
I’m happy to announce that after months of intensive development and testing, I’m finally ready to introduce a developer preview of the new Virtualmin Podman plugin. It’s now available for testing for all Virtualmin Pro users.
To install it on EL systems:
curl -u 'SERIAL:KEY' https://download.virtualmin.dev/webmin-virtualmin-podman-latest.rpm -o /tmp/webmin-virtualmin-podman-latest.rpm
sudo dnf install /tmp/webmin-virtualmin-podman-latest.rpm
and for Debian and its derivatives:
curl -u 'SERIAL:KEY' https://download.virtualmin.dev/webmin-virtualmin-podman-latest.deb -o /tmp/webmin-virtualmin-podman-latest.deb
sudo apt-get install /tmp/webmin-virtualmin-podman-latest.deb
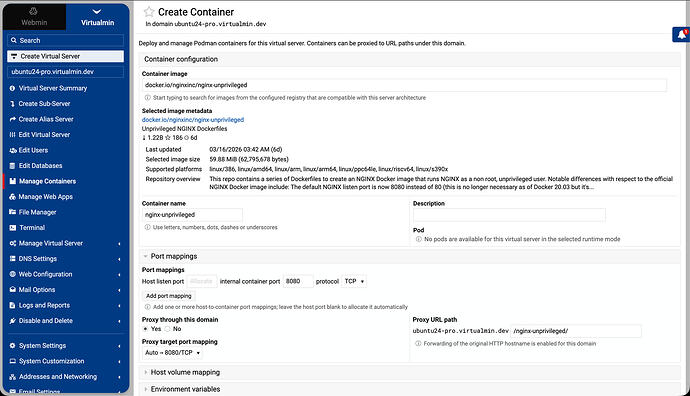
After the installation is complete, the plugin should be enabled globally on the “System Settings ⇾ Features and Plugins” page. Once this is done, it should also be enabled individually for each domain using the “Edit Virtual Server” page.
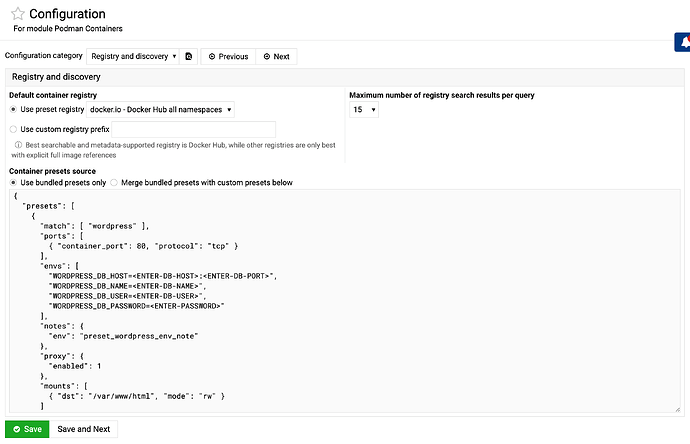
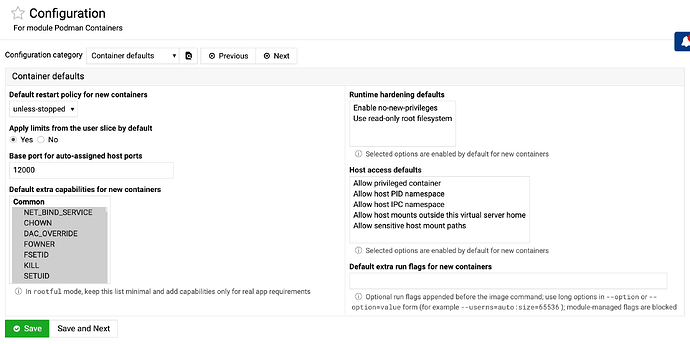
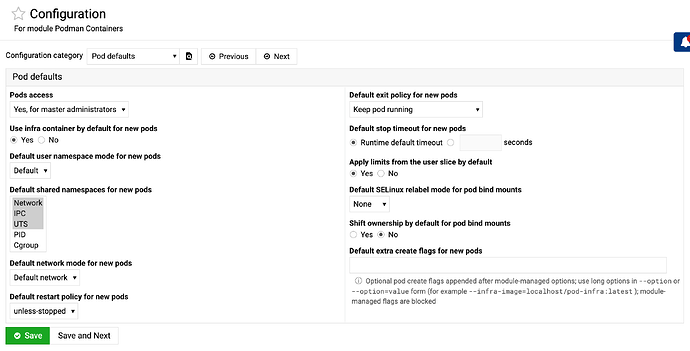
I tried to make it as simple as possible, but the module config has an intimidating number of options and can enable advanced features that are disabled by default. It’s designed to be simple out of the box but powerful for advanced users.
Note that we are open to constructive suggestions, and changes can be made before the final release.
README.md
Virtualmin Podman Plugin
Virtualmin Podman plugin for deploying and managing Podman containers and pods
per virtual server, with integrated networking, proxying, runtime controls,
logs, and browser terminal access.
Overview
This module adds Podman management to Virtualmin domains and to the global
Virtualmin explorer. It supports both container and pod workflows, runtime-
aware rootless and rootful execution, reverse proxy integration, image
discovery, reusable defaults, and browser-based troubleshooting tools.
Current features
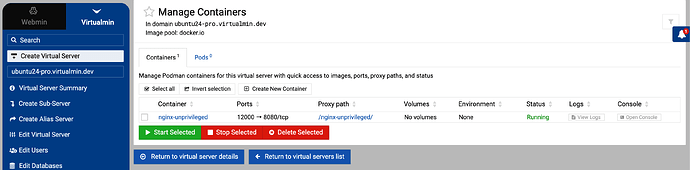
Containers
- Domain-scoped management view for each virtual server
- Global cross-domain container explorer
- Install, edit, save/reinstall, start, stop, restart, delete, and bulk
lifecycle actions - Configurable list columns for ports, paths, volumes, envs, status, logs,
console access, and optional runtime usage stats - Quick links to logs and terminal console from list and details views
- Runtime metadata and inspect summaries for troubleshooting
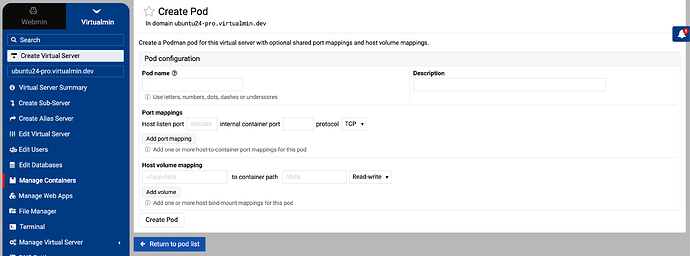
Pods
- Per-domain and global pod tabs with configurable columns
- Create, clone, view, start, stop, delete, and bulk lifecycle actions
- Pod details view with member container summaries
- Pod-level logs view plus member-container logs and console links
- Support for creating containers directly inside an existing pod in the
matching runtime context
Runtime modes
- Image user (
rootless) [default]: Podman runsrootlessas the virtual
server owner, and containers keep the image’s own user model - Domain user (
rootful): Podman runsrootful, and containers run as
the virtual server UID/GID
Runtime mode policy can be exposed as a selector, shown as a fixed note, or
kept hidden while still applying the configured default. Separate Podman
runtime contexts are respected for container discovery, pod discovery, and
network selection.
Networking and proxying
- Multi-port host-to-container mappings with TCP or UDP
- Pod-level port publishing for shared pod frontends
- Automatic host-port allocation from a configurable base
- Optional reverse proxy path mapping for containers and pods
- Proxy target port selection
- Proxy host-header forwarding policy support
- Pod network modes:
- Default network
- Specific Podman network
- Host
- None
- Inline create and delete of Podman networks in the selected runtime context
- Advanced pod network options:
- network aliases
- static IPv4, IPv6, and MAC where supported
- DNS servers, search domains, and resolver options
- extra host entries
- no-hosts and no-resolv controls
Storage, environment, and security
- Multi-volume host path mappings with
rwandro - Pod bind mounts with SELinux relabel and ownership-shift controls
- Domain-home path controls for non-admin contexts
- Environment variables as
KEY=VALUE - Extra Linux capability controls
- Runtime hardening flags such as
no-new-privilegesand read-only root
filesystem - Host access controls for privileged mode, host namespaces, and sensitive or
outside-home mounts
Resource limits and health checks
rootfulruntime only for explicit container resource controls- Memory, swap, reservation, CPU, PID, cpuset, shared memory, blkio/device
throttling, and ulimits where supported - Optional cgroup-parent mode to inherit limits from the user slice
- Pod CPU, memory, and shared-memory defaults and limits
- Container health command, interval, timeout, retries, start period, and
failure policy - Container restart policy and pull behavior
- Pod restart policy, exit policy, stop timeout, infra container, user
namespace mode, and shared namespace controls
Image discovery and defaults
- Registry search UI with keyboard navigation
- Metadata fetch for selected images
- Architecture compatibility checks
- Defaults resolution from:
- local
podman image inspect - remote
skopeo inspect --config - bundled
presets.json - optional custom presets JSON from module configuration
- local
- Preset and metadata hints for ports, mounts, envs, health checks, and proxy
behavior
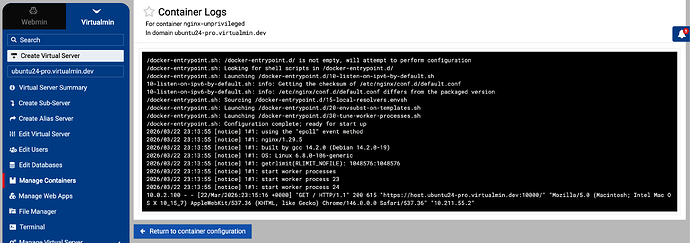
Logs, console access, and list views
- Container log viewer
- Pod log viewer
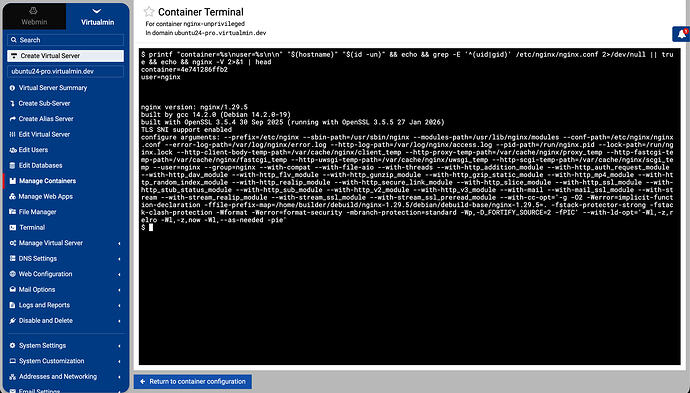
- In-container interactive terminal shell
- Integrated with Webmin xterm backend
- Domain and container context shown in terminal header
- Global and per-domain list views for both containers and pods
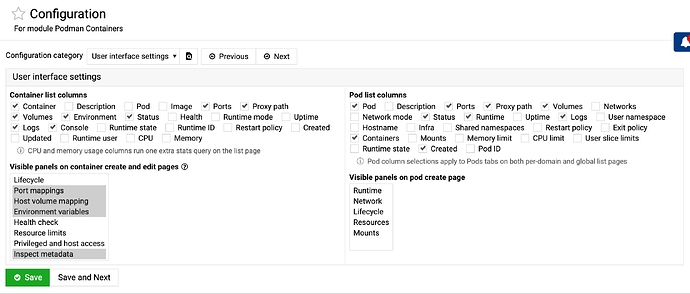
Access control and UI defaults
- Owner and reseller access controls
- Separate pod access policy for master administrators, all users, or disabled
- Configurable default list columns for containers and pods
- Configurable visible panels for container and pod create workflows
- Module-level defaults for runtime mode, restart behavior, networking,
security, mounts, extra Podman flags, and other create-time behavior
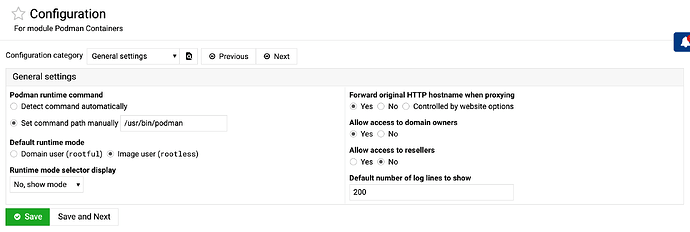
Module configuration
Config is organized into:
- General settings
- Podman command path
- owner and reseller access
- pod access policy
- default runtime mode
- runtime mode selector display
- proxy host-header policy
- default log lines
- User interface settings
- default container list columns
- default pod list columns
- visible container panels
- visible pod panels
- Registry and discovery
- default registry pool
- search result limit
- presets source mode:
- use bundled presets only
- merge bundled presets with custom presets JSON
- Container defaults
- restart policy
- base auto-port
- user-slice cgroup-parent behavior
- default extra run flags
- default capabilities
- default hardening options
- default host access options
- Pod defaults
- infra container and user namespace mode
- shared namespaces and network mode
- restart, exit, and stop-timeout policy
- user-slice limits, CPU, memory, and shared memory defaults
- mount SELinux and ownership-shift defaults
- default extra create flags
Presets
presets.json supports curated defaults for known images, including:
- recommended volume targets
- recommended env variables
- recommended port and proxy hints
- optional notes shown in the UI
Custom presets entered in module configuration are saved in:
/etc/webmin/virtualmin-podman/presets.json
When custom mode is enabled, bundled and custom presets are merged and custom
rules take precedence over bundled rules for matching entries.
If the custom file is empty or invalid, bundled presets are used.
Requirements
- Virtualmin Pro with this plugin installed and enabled
- Podman installed on the host and reachable by the configured command path
skopeorecommended for remote image metadata lookups- Webmin
xtermmodule for browser console access - Reverse proxy feature enabled on domains that need proxied container or pod
paths
Notes
rootlessbehavior depends on host capabilities and user-session or systemd
setup- Runtime capability and cgroup behavior can differ between
rootfuland
rootlessmodes - Some static network addressing and resource controls are only available in
supported runtime or network combinations - Downloaded image listings, pods, and Podman network choices are runtime-
context aware - Enabling CPU and memory list columns adds an extra runtime stats query