I am on a 7.50.0 that started as a 7.4x. I noticed today that Fail2Ban didn’t have an apache-auth jail (which I do on an other Virtualmin but don’t remember configuring personally, though that does not mean that I didn’t). Either way I did not setup the jails that are there now (dovecot, postfix, postfix-sasl, proftpd, sshd, webmin-auth).
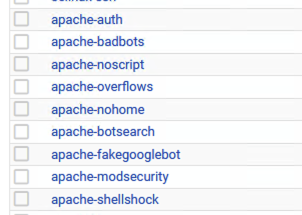
I apologize if this is a question that belongs I a forum dedicated to Fail2Ban, but I noticed the plethora of options for apache stuff under:
Webmin > Networking > Fail2Ban Intrusion Detector > Filter Action Jails
… is there any reason I wouldn’t want all of these enabled?
Thanks.
| SYSTEM INFORMATION | |
|---|---|
| OS type and version | Ubuntu 24.04 |
| Virtualmin version | 7.50.0 |