| SYSTEM INFORMATION | |
|---|---|
| Ubuntu Linux 20.04.6 | REQUIRED |
| Webmin version 2.021 | REQUIRED |
My webmin log has hundreds of entries like these:
1681426868.252354.0 [14/Apr/2023 05:01:08] root - 94.45.158.43 global miniserv.pl "failed" "-" "wrongpass"
1681426872.252357.0 [14/Apr/2023 05:01:12] root - 94.45.158.43 global miniserv.pl "failed" "-" "wrongpass"
1681426877.252360.0 [14/Apr/2023 05:01:17] root - 94.45.158.43 global miniserv.pl "failed" "-" "wrongpass"
1681426883.252363.0 [14/Apr/2023 05:01:23] root - 94.45.158.43 global miniserv.pl "failed" "-" "wrongpass"
1681430070.256274.0 [14/Apr/2023 05:54:30] root - 68.183.170.227 global miniserv.pl "failed" "-" "wrongpass"
1681430074.256277.0 [14/Apr/2023 05:54:34] root - 68.183.170.227 global miniserv.pl "failed" "-" "wrongpass"
1681430079.256282.0 [14/Apr/2023 05:54:39] root - 68.183.170.227 global miniserv.pl "failed" "-" "wrongpass"
1681430085.256299.0 [14/Apr/2023 05:54:45] root - 68.183.170.227 global miniserv.pl "failed" "-" "wrongpass"
1681430093.256302.0 [14/Apr/2023 05:54:53] root - 68.183.170.227 global miniserv.pl "failed" "-" "wrongpass"
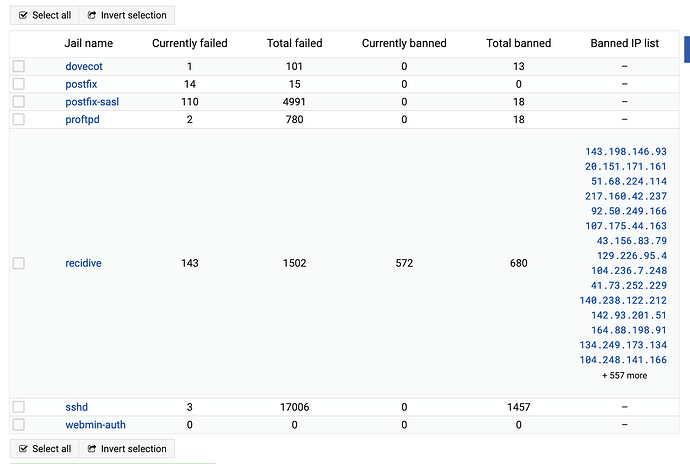
I think fail2ban should take care of these. How can there be so many repeated attempts?
Fail2ban is set to start at boot, but I haven’t changed any of its configuration.
Is there anything the admin should do here?
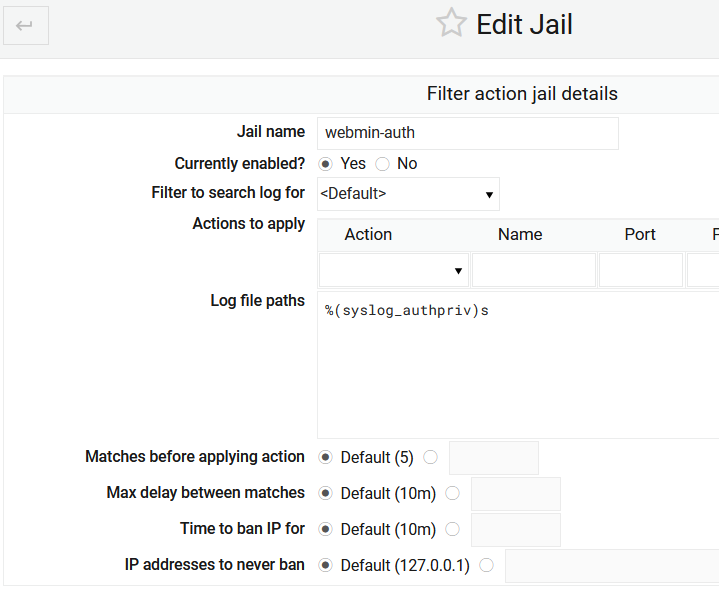
For example, the webmin.auth Jail is active, but there is no “action” set:
Should I set one? Which?