Just a heads up. This is a pretty crazy story.
interesting even though i am not a WP advocate it is a concerning tale for all PHP and potentially other app users.
the statement at the end
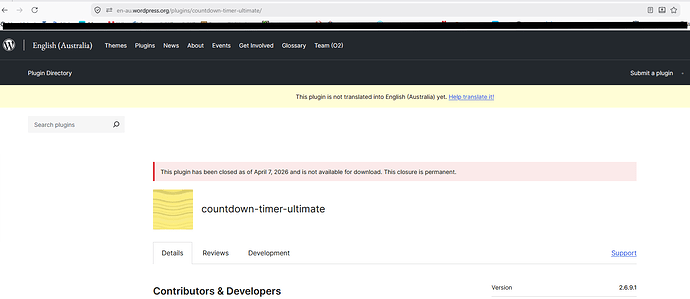
```The WordPress plugin marketplace has a trust problem.```
being the most pertinent.
maybe not. I don’t use wp for the reason of nightmare stories like this, but if wp are responsible for distributing the plugin the blame is with them for not reviewing updated code. when I use a cms type system I use mybb to which I write all the plugins used or if I need to use one of mybb’s large plugins I will do a complete review of the code to try and find any naughty code in there, to date I’ve never been burned.
there is a lot to be said for doing that.
but in these days of AI coding, global teams and “free” code it is all to easy and quick to open the door to let the bots in.
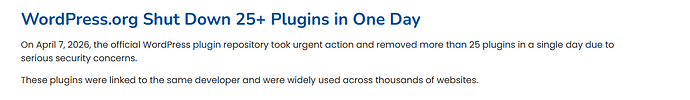
I think you’re taking the wrong lesson if you’re looking at it as a problem for WordPress, specifically. All supply chains of this sort are vulnerable to bad actors…especially bad actors that are able to take over historically known-good projects. This has happened many times in the npm (NodeJS), pypi (Python), and other ecosystems, too. You don’t have to be a WordPress user to worry about supply chain risk.
I think WordPress is maybe more prone to more widespread damage for two reasons: It’s the most popular way to build a website (driving about half of websites, last I heard), and it’s used by mostly non-technical people. It’s like Windows…a perfect storm for security exploits, because it’s everywhere and it’s used mostly by folks who probably won’t find out about exploits until it’s too late.
The WordPress folks response was good, as far as I can tell. As I understand it, they explicitly tried to repair exploited systems with an update, which is unusual. I guess the fallout must have been pretty wide for them to go that far.
Anyway, “WordPress bad” is the wrong lesson to take from this. WordPress does scan incoming modules listed on their marketplace thing. But, scanners often only catch old stuff. A new implementation of an exploit can look harmless without deeper analysis. LLMs are turning out to be pretty good at finding security bugs (though, also, in my experience, even better at inventing security bugs out of thin air…false positives are really high with LLM security scanning), so maybe things will get worse for a while (as bad actors are always the first to adopt risky new tech) and then better eventually (as the tools get more reliable and more widely used).