with my main domain I initially use the COPY TO to button for the main domain (and don’t ever use it for other domains)
Please note that I do NOT use LetsEncrypt certs for my mail server systems. They are not recognized and from what I have read will not become EV or OV certs so will not be accepted by many or maybe all email client softwares. That why I buy a cert.
I’m left with how are my EV cert keys getting overwritten when they are completely outside of any domain’s file structure?
At the moment, any client I suppose can log in and run a LetsEncrypt renewal which is a bad situation when it takes down smtp, imap and pop services, or at least throws them into using the wrong cert which email clients complain about and would require a scary override for them. “Who the heck is ‘somedomain’ and why are they into my email program?”
Joe,
I did install I believe it was certbot when we had the last LetsEncrypt issue a few months ago. I was getting extremely close to needing renewals so I installed the following:
Description certbot is a free, automated certificate authority that aims
to lower the barriers to entry for encrypting all HTTP traffic on the internet.
Package certbot Class Unspecified
Version 1.3.0-1.el7 Vendor Fedora Project
Architecture noarch Installed 03/30/2020 11:17:29 AM
I have that on the 2 affected systems. But again, so far only 3 certs needed updates which happen to all be on CentOS 7 systems.
I did not uninstall it as I didn’t know if Virtualmin may also need that package. That’s about the only fly in the soup that I can think of on these systems.
John
Joe
I raised a ticket with some information from my system.
I use Lets Encrypt and when a certificate auto renewes the SSL cert from that domain gets copied to main server ssl (at least for Dovecot)
Brian
On the first server where this problem occurred, I deleted the ssl entries within dovecot.conf for that first offending domain.
Results:
- Before SSL cert said this cert was already being used by Dovecot.
- Deleted the entries.
- Dovecot would not restart. I believe lots of processes running maybe under these other/alternate certs?
- Rebooted the system and Dovecot started fine.
- The notice in SSL cert for the domain was gone.
Results:
Apparently on CentOS 7 systems the use of the cert is determined by looking at dovecot.conf? It seems like ssl.conf may have been a better place?
Rebooting the system is never fun during prime hours.
I still would like to know what sets a renewal to overwrite the main server keys in /etc/pki/tls
I haven’t found reference to this yet.
John
I’m still poking around on a CentOS 7 system:
The 2nd cert that updated has this message under:
Virtualmin -> The Donain’s Account -> Server Configuration -> SSL Certificate -> SSL Certificate
This SSL certificate is already being used by : Webmin (thedomain.com), Usermin (host thedomain.com), Dovecot (host thedomain.com)
I am positive that I never set this cert to be used by all of those services.
These are the entries placed into dovecot.conf:
local_name domain.com {
ssl_cert = </home/domain.com/ssl.cert
ssl_key = </home/domain.com/ssl.key
ssl_ca = </home/domain.com/ssl.ca
}
local_name www.domain.com {
ssl_cert = </home/domain.com/ssl.cert
ssl_key = </home/domain.com/ssl.key
ssl_ca = </home/domain.com/ssl.ca
}
Looking at some of the other entries, I notice that the ssl_ca entry doesn’t exist. These are all further up the list so I suspect entries made earlier under almost certainly an older version of Webmin/Virtualmin.
joe i wasnt trying to start a discussion about php-fpm. If you correctly read my post above, you will see that i said that the latest webmin update has caused two issues on my system (and i briefly described the issues). That is not hyjacking a thread BTW just in case you were thinking this.
In terms of the SSL certificate issue and the php-fpm issue, my point was…
WEBMIN UPDATES ARE OVER WRITING EXISTING SYSTEM SETTINGS THAT IT SHOULD NOT BE OVERWRITING!!!
do you understand what i am trying to say??? (the php-fpm configuration issue has been a problem on my system for more than a year and yet after my repeated complaints about it, the issue still keeps occuring with specifically webmin update.
This entire thread is essentially about the webmin update…there is something about the SSL module that isnt working correctlly as most systems were working fine before the update completed! (whether its something that has existed previously i havent a clue, im not a programmer all i see is the end user experience and frustration)
To echo what others above have stated, as far as i can tell:, my email server issue had the following basic symptoms:
- my mail logs did not seem to contain any useful information that helped me problem solve
- it appeared that usermin was working normlly, only email client applications such as outlook/apple mail were throwing errors
- From my initial testing, it appeared that client apps were able to send emails but not receive them so i suspected it was dovcot with the problem. From reading the above posts about dovcot over writing the email server domain SSL cert this does seem to make sense to me
- I was unable to access Webmin after trying to “Issue a new Letsecrypt ssl cert” (it just kept losing connection in my browser after just a few seconds of logging in) so the problem is more than just email related)
- I have system monitors setup in virtulamin…none of these automated monitors even sent me an email saying something was wrong until after Webmin access was lost hours after the original SSL problems with email clients started (and that reflects what i said about there being basically nothing in the logs)
I was forced to rebuild my system…sure i could have accessed it through putty, but becuase of the wide variety of issues, i simply cannot have a production system offline for 4 or 6 hours whilst i try to figure out why a webmin update screwed it up when i can rebuild it from a backup in about 15-30 minutes!
Please understand, i am not trying to be anti virtualmin. I absolutely love this program and the more i use it the more i appreciate the product you guys have created. I guess in my liking the program so much, i treat it (and its developers) with a bit more “family emotion”.
So the question is…how is this SSL overwriting the host cert to be resolved?
Could i also ask…would separating the mail server from webhosting accounts have made any difference to the SSL cert issue?
kind regards
Adam
@adamjedgar I understand you’re frustrated, and I’m sorry you’ve gotten hit by a couple of different problems. I’m trying to sort out both problems, but they aren’t related. When threads get chaotic it becomes impossible for me (and especially Jamie, who has even less time than me to dedicate to the forums) to figure out what is going on and solve it. If we want to solve any problem, rather than just talk about it, we need to isolate the issue and reproduce it. I simply don’t know how to solve any of these problems until I understand them.
I have the same problem with auto-renewal letsencrypt and Dovecot.
When an auto-renewal (or manual renewal or even on a new certificate) occurs, the main SSL cert and key of the Dovecot are replaced from the new SSL certs!!!
Hi Joe, sorry i can see how my adding that information makes your job harder. I keep forgetting you guys arent gods (hehe).
Ok so the exact symptom that i need to resolve right now is the following…
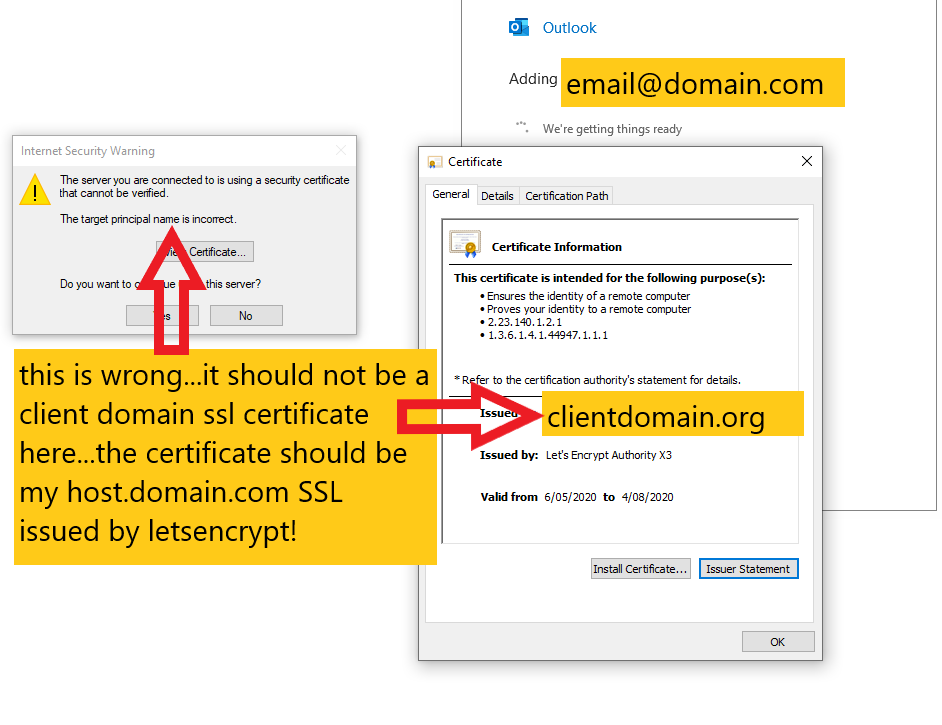
when i attempt to connect Outlook email client on my desktop pc with an email account on my virtualmin server, I am presented with the wrong SSL certificate (its one of the certificates for a client virtual server…this is a shared hosting system with just 1 ip address).
How do i
- stop webmin from allowing client domains in virtualmin to over write the host SSL certificate for the email server and webmin
- remove the incorrect ssl certificate from postfix and dovcot servers is webmin? (webmin and the email server should not be using a clients SSL certificate for shared hosting…its supposed to use the one issued to hostname.myprimarydomain.com)
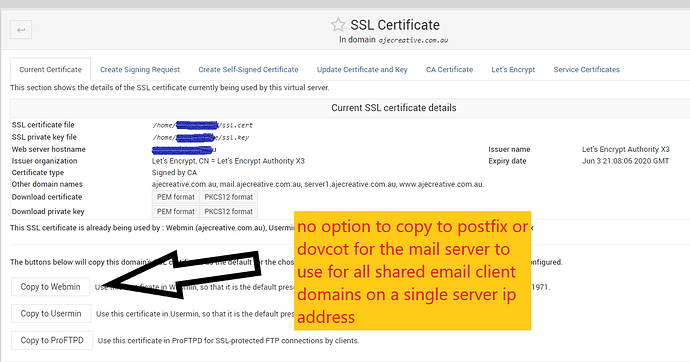
I cannot get virtualmin>Server configuration>SSL Certificate to give me an option to "Copy SSL to postfix or dovcot…see below
what happens if you run the Request Certificate again ?
ps. Joe thanks ! your help on this, we know how difficult it is to glean the right information from the sparse details we post :o)
I’m worried running the Request Certificate will stop with too many attempts.
Anyway, I backed up teh domain SSL files. Issue happened again. so I copied back the SSL files,
restarted Dovecot and apache and I’m back running again.
best thing to do in short term is to check the ssl files with a script and if changed copy the backup files
Ilia tracked down the culprit.
In short, my build scripts had a bug where it pulled the latest git code, and didn’t checkout the tagged version (build processes have been completely re-done over the past couple months). This meant the code in question had some changes related to allowing newer versions of services to manage per-domain certs much better…but, that code isn’t finished, so it behaves badly.
I’ve rolled back to the tagged version (which is what should have been released in the first place), and released 6.09-3 with the correct code.
Apologies for the troubles. This bug has been fixed in my build scripts, so this kind of problem won’t happen again.
Note there were a few bugfixes and improvements that snuck out into the wild with the previous package that have now been rolled back…there was no quick way to selectively keep some changes, and this issue seemed more pressing than any of the other fixes in that batch. We’ll do a 6.10 soon (or I’ll cherry pick the good bits when I have time to actually read all those additional commits).
Will this roll back stop it from adding cert paths for every domain in the dovecot.conf file? We don’t advertise that to our end users, but I fear some may have accidentally tripped onto it. As the Postfix version on CentOS only allows one domain and therefore only one cert, we have defaults to our main domain for both incoming and outgoing.
Also, the last I could find on LetsEncrypt is that they do not support the cert type required by most email client programs and it said they have no plans to do that. So I’m not sure why the options for dovecot and postfix exist? I suppose they would work for small systems where exceptions would be expected?
Could you open a new topic about this question with specific details about what you mean? (i.e. what mail clients, what issue(s)?) It’s a different set of problems, and not something I have expertise on without doing some research.
Joe
Thanks very much for your efforts, we’re all developers and we know the pain at times 

I  virtualmin
virtualmin
Brian
@Joe I should know this … how do I tell on my RedHat 7 server from
yum list wbm-virtual-server
if I will get your 6.09-3 kit … or the 6.09-2 (?) bad one ?
Verne
It only effects Pro packages. If you’re on GPL, there is no 6.09-3 (or 6.09-2).
THANKS … I feel better !!
Verne